What Small to Mid-sized RIAs Need to Know About the SEC's Updated Regulation S-P
The SEC’s amended Regulation S-P takes effect for small to mid-sized registered investment advisors on June 3, 2026. If you haven’t started preparing, now is the time. This post breaks down what the rule actually requires, where small firms most often fall short, and how the SEC’s examination staff will evaluate your compliance, including some less obvious areas of inspection that SEC Examiners have mentioned during their January outreach event.
A Quick Recap: What Changed and Why It Matters
Regulation S-P has been on the books since 2000, governing how investment advisors, broker-dealers, and other financial institutions protect clients’ non-public personal information. The original rule covered physical and digital records alike. However, in 2024 the SEC finalized amendments that significantly expand those obligations.
- A formal incident response program with documented policies and procedures
- A client notification requirement when sensitive information is breached
- Expanded service provider oversight obligations, including a 72-hour notification requirement for all vendors
- A requirement to maintain written records documenting compliance with the safeguards and disposal rules
Compliance Deadlines
Large firms (AUM ≥ $1.5B): December 3, 2025 — already in effect.
Small to mid-sized firms (AUM < $1.5B): June 3, 2026 — your deadline is approaching.
Not Sure Where to Start?
With the June 3rd deadline two months away, we are offering free 30-minute consultations for firms that are not sure where to start. SIMAPTIC was built specifically to give RIAs access to the kind of automated security testing that was previously only available to organizations with enterprise budgets. Book a call to walk through your current setup with one of our experts and identify your most pressing gaps.
Schedule a Free ConsultationDocumenting Security Practices
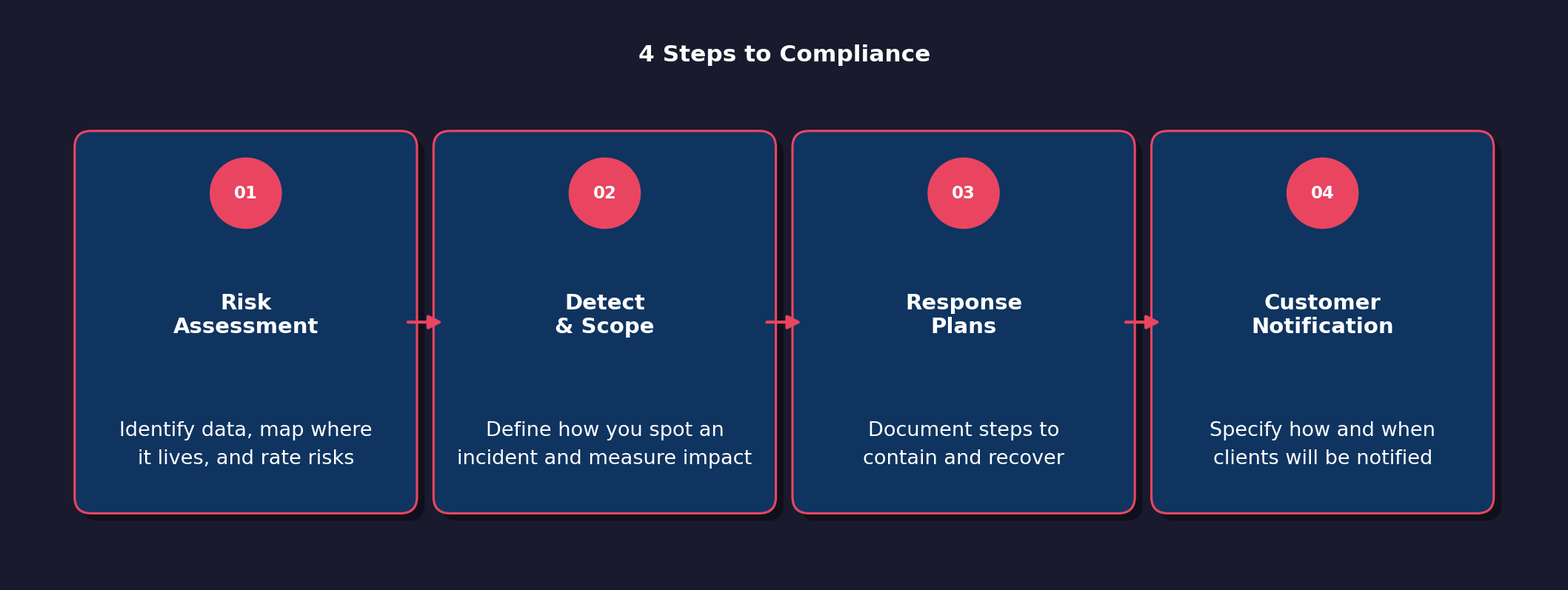
The most substantial new requirement is what the SEC refers to as an incident response program. The new amendments require that RIAs document a program that is “reasonably designed to detect, respond to and recover from unauthorized access.” This essentially means that RIAs need a full cybersecurity plan and not just a course of action on how you will notify clients. Luckily, SEC Examiners are aware that what this plan looks like will vary dramatically based on the size and resources of each RIA and they plan to “right size” the examination. Following the steps below should provide you with an excellent starting place for compliance:
1. Perform a Risk Assessment
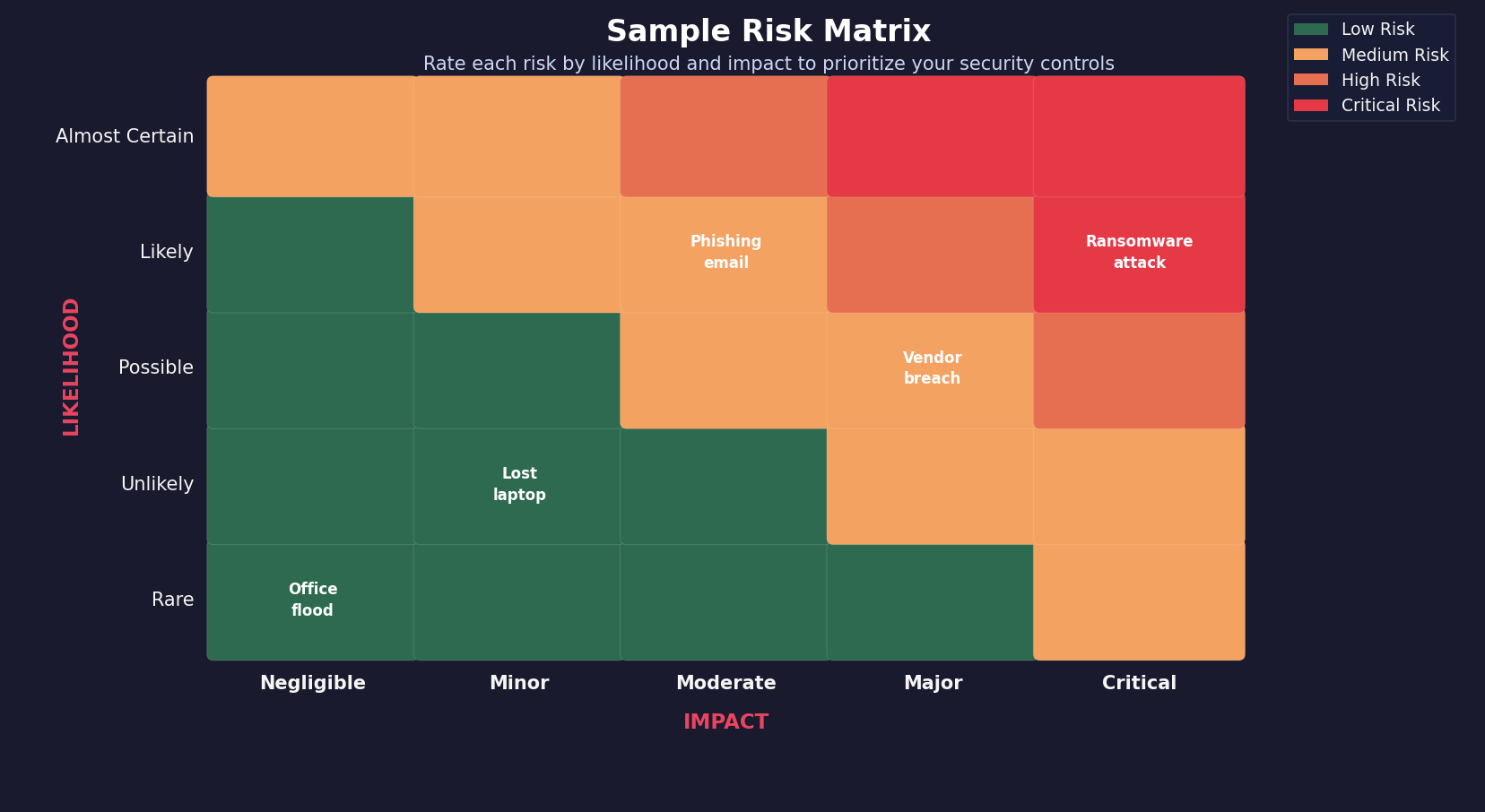
Not only is a risk assessment the first step to understanding what security controls will be considered “reasonable” for your organization, but SEC Examiners have explicitly stated that they expect at the very least to see a risk matrix including not only business risk but security/IT risks as well. A risk matrix is also the best way to justify any controls you have chosen not to implement. For example, if you are a one-person shop that has all your client data stored on third-party platforms, you have minimal risk associated with your organization’s network, and the risk matrix would provide the justification for not adding additional security controls to it.
One of the most important first steps is to identify the types of sensitive data you handle. Start by reviewing all handled data that may meet the SEC’s definition of sensitive information. The SEC defines this as any data “that alone or in conjunction with any other information, the compromise of which could create a reasonably likely risk of substantial harm or inconvenience to an individual identified with the information.” That’s not the easiest definition to understand, so we like to ask ourselves “if we informed a client that this information had been compromised, would they be upset?” as a more intuitive way to interpret it. The SEC has explicitly called out examples such as SSN and account numbers, but most interpretations also include data such as home address and email addresses as potentially sensitive.
Once you have identified all the sensitive data you handle, you should map it to where it is stored and handled. This step is really important because one of the largest pitfalls we see is companies stating that they don’t store sensitive client data when in reality they are storing files that include it. Often they believe that because they handle all client interactions through third-party platforms like CRM and portfolio management platforms that they are not storing data. But if they then save correspondence data on a file share, they are in fact putting that data on their local network. This doesn’t mean that the data is inappropriately stored, but without a thorough understanding of where data resides, your risk matrix will be inaccurate.
While the regulation does not require that you use any specific risk management framework, the SEC Examiners have recommended the NIST Cybersecurity Framework. NIST provides a plethora of documentation on everything from conducting risk assessments to security control management.
Do You Know Where Your Client Data Actually Lives?
This is one of the most common gaps we see in practice. Firms that are confident all their client data lives on third-party platforms often find during a review that they are also storing it locally on file shares. SIMAPTIC can scan your network and identify what is there and where it resides. The results map to NIST controls and give you a documented starting point for the risk matrix examiners will ask to see.
See What's on Your Network Learn More2. Define How You Detect and Scope the Impact of an Incident
One of the nuances in what the SEC wants to see in incident response plans is how you will detect a breach. This ties into two key points for the SEC. First, they want to ensure that RIAs will provide timely notification to their clients should a breach occur. Without an ability to detect an intrusion, how can an RIA ever know when to notify customers?
Second, the ability to detect an intrusion or abnormal access to customer data directly ties to the ability to determine the scope of the incident. One of the key details the SEC expects to see is a documented process for how you determine if sensitive customer information was accessed. It’s also important to note that if you have a cybersecurity incident but determine no sensitive client data was accessed, you are still expected to retain records of the incident along with the detection artifacts that allowed you to make that determination.
This may sound daunting, but for many RIAs the detection and identification will be relatively straightforward. For example, if you use a managed service provider (MSP), you can document that you expect the MSP to detect and notify of a breach and its scope. If you have an IT department, then the policy should identify who is responsible for analyzing the data and what your sources of data will be. The policy should also identify who is responsible within the organization, and who is responsible for making the decision to notify customers or not.
3. Create Response Plans
Your policies should describe the steps you take to stop the incident from progressing if still in progress, such as isolating affected systems, cutting off unauthorized access, and notifying the right people internally.
This part of the plan will flow from the previous step and, just like before, for many shops you will be able to offload a lot of the details to your MSP. Just ensure that you get detailed information from them on how they plan to execute responses to an incident.
You can also leverage your standard business continuity plans that you have likely already produced, such as how you will continue operations if you lose email or phones. These can be directly referenced in your cybersecurity response plan as to how you will conduct operations during an ongoing incident.
4. Document How Affected Customers Will Be Notified When Required
This section does not need to be long but should identify how you plan to notify clients. Will it be via email or a phone call? Will there also be letters going out? It should also document what information you plan to provide clients about an incident and any additional services you may offer to help protect them from any repercussions of the exposed data.
Incident Response Plan Recap
The SEC isn’t necessarily looking for a 50-page document from every RIA. For a solo advisor or a small firm, your policies should reflect your actual operations. That means documenting if you use any malware detection software and what you are doing to respond to any alerts you may get from it. If you are a slightly larger firm, make sure that it includes the technical information for implemented security controls and clearly lays out roles among the staff you do have.
The biggest thing, no matter what you do, is to make sure you document it. The SEC examiners have repeatedly stated that they want to see proof of implementation of your plan. They have seen too many plans that look good on paper but when they attempt to validate them, the plans are not actually being followed.
Key Quote from the January SEC Outreach Session
Sal Montemarano, the SEC’s senior specialized cybersecurity examiner: “It’s not just what’s written for us. It’s written and executed in the office.”
The Customer Notification Requirement
Not every security incident triggers a customer notification. The rule draws a line between “customer information” and “sensitive customer information,” and only the latter triggers the notification obligation.
Sensitive customer information includes things like Social Security numbers, account numbers combined with passwords or access codes, and other information that, alone or in combination, could be used to authenticate someone or access their accounts.
State-Level Requirements
If you are handling clients in California or Massachusetts, you likely have additional data protection requirements under the California Consumer Privacy Act or 201 CMR 17.00, which have even broader definitions of what is considered sensitive data.
30-Day Notification Window
If sensitive customer information was accessed or reasonably likely to have been accessed without authorization, you have 30 days from becoming aware of the incident to notify affected individuals. That notice must include details about the incident, what information was involved, and steps customers can take to protect themselves (such as how to obtain a free credit report).
The 30-day window is to give RIAs time to determine the extent and scope of the incident. If after initially declaring an incident within the organization, you complete a reasonable investigation and you can affirmatively determine that the sensitive information has not been and is not likely to be used in a way that causes substantial harm, notification may not be required. But if the investigation is inconclusive, you must send the notice. If you can’t determine which customers were affected, you must notify all clients whose sensitive information resided on the compromised system. There are a handful of exceptions that allow for a longer disclosure period, but they are edge cases and you should plan to always comply within the 30-day period.
Service Provider Oversight: Where Small Firms Are Most Exposed
The change that has raised the most concern within the industry is the new third-party oversight requirement that requires third parties to notify the RIA within 72 hours of an incident. Most small RIAs rely heavily on third-party vendors for a variety of purposes such as custodial services, CRM platforms, email, IT support, and cybersecurity monitoring. Under the amended Regulation S-P, that reliance doesn’t reduce your compliance obligations. It shifts some of the work, but not the responsibility.
Here is what the rule now requires:
Verify Third-Party Data Handling: Under the amendment, RIAs are ultimately accountable for client data that may be compromised during a breach at a third-party vendor. This means that your policies and procedures need to include how you will verify that vendors are compliant with your data handling policies.
Service providers must notify you within 72 hours of becoming aware of a breach: This part of the amendment is the crux of concern for most RIAs. The reality is that most large third-party vendors such as Fidelity, Schwab, or Microsoft already have data handling policies that will meet the SEC’s requirements, but most RIAs with existing contracts do not have clauses requiring 72-hour notification.
Good News and Bad News on the 72-Hour Rule
Bad news: The SEC has confirmed this requirement applies to all third-party vendors with no carve-outs and no exceptions for existing contracts.
Good news: The 72-hour notification does not have to appear as a contract clause — you can ask vendors to confirm in writing that they will meet this requirement. A documented plan to meet the mandate may be sufficient.
During public Q&A sessions, the SEC has been directly asked about this, and each time they have punted on giving direction on how to proceed with remediating existing contract gaps. They have recommended reaching out directly to speak with an examiner about individual circumstances. At the very least, you need to have performed a gap analysis on what vendors you have that will not be able to comply and have a documented plan for remediation, even if it’s simply to renegotiate at contract renewal.
You remain ultimately responsible for ensuring customer notification happens, even if you’ve entered into a written agreement delegating that task to the service provider. Contracts can authorize the provider to send notices on your behalf, but if they don’t, the failure is yours.
How the SEC Will Examine Your Firm
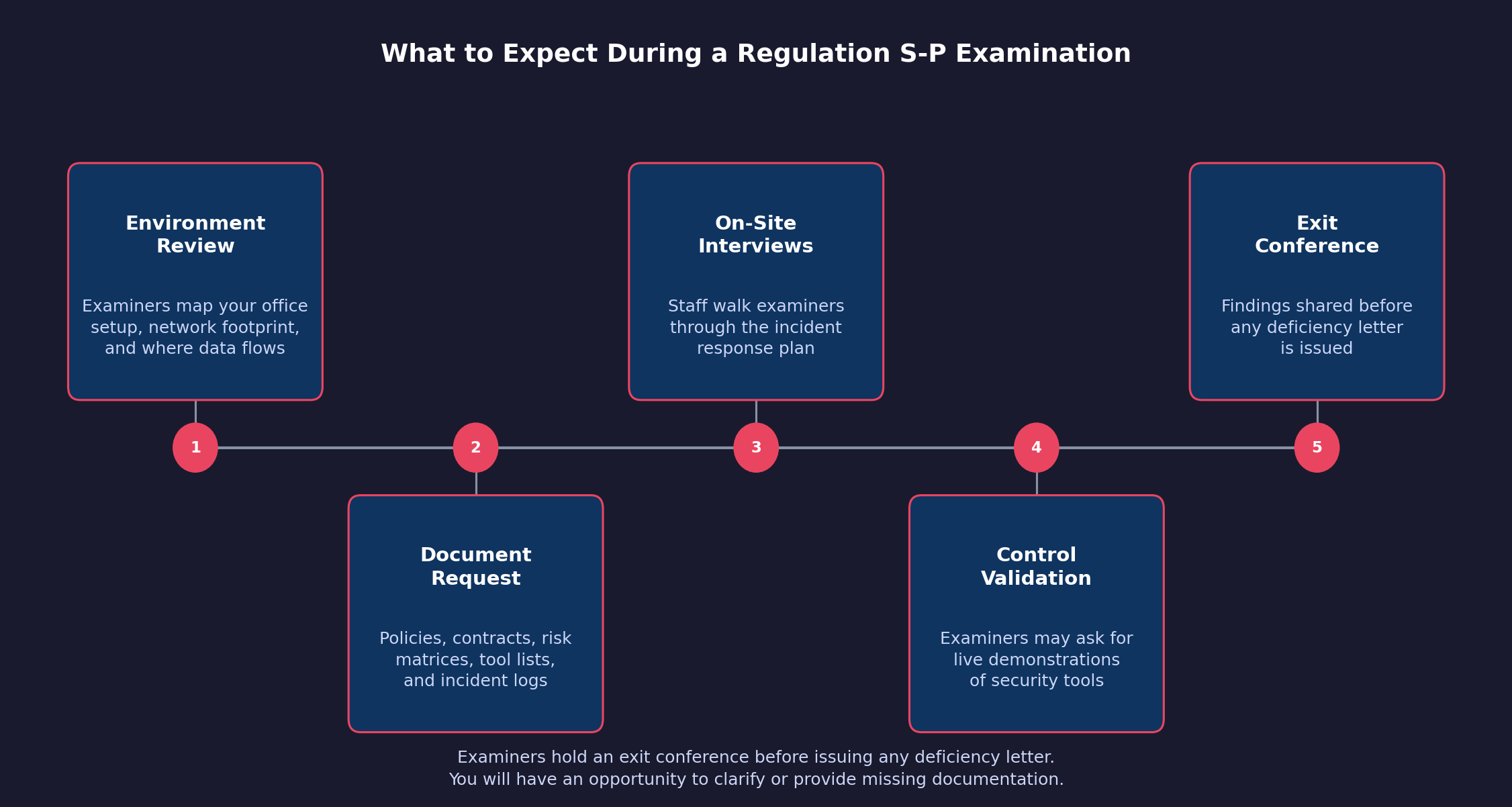
The SEC’s Division of Examinations has provided basic outlines about how they plan to approach Regulation S-P exams for small firms. Here’s what to expect.
They’ll start with your environment. Examiners will want to understand your office setup, network footprint, where client data actually lives, and how it flows through your systems. This is where the data identification and mapping we mentioned in the previous section will come into play. If you tell them that you store no sensitive data because it’s held by third-party data custodians, they will want to see documentation backing that assertion.
They’ll request specific documentation. An initial document request for an incident-response-focused exam will typically include your written policies and procedures, your service provider contracts, organizational charts, any risk matrices you’ve developed, a list of tools used for monitoring and detection, and documentation of any incidents that occurred during the review period. They have mentioned that they may also request logs demonstrating that your detection tools are actually functioning, citing that they have seen many RIAs who have purchased tools but never properly implemented them.
They’ll conduct interviews, often on-site. Examiners prefer to visit in person. They’ll talk to whoever handles compliance, IT, and operations. In a small firm, that may be one person wearing several hats. This is where they will attempt to establish that you are actually implementing your written policies and procedures by asking personnel to walk through the incident response plan and reviewing artifacts from security tools. Examiners have mentioned that they may ask personnel to demonstrate how security controls on the network work.
They’re not trying to catch you. The SEC’s examination staff was direct on this point during their compliance outreach: the exam process is designed to confirm compliance and add value, not to create gotcha moments. Before issuing any deficiency letter, examiners will hold an exit conference and give you an opportunity to clarify or provide documentation they may have missed.
The examiners noted the three most common findings in the Regulation S-P space are:
Top 3 Exam Deficiencies
- Policies and procedures don’t exist. Follow the above guide and ensure you have at least basic policies in place.
- Policies and procedures aren’t reasonably designed. Policies need to actually address identified risks specific to the RIA and go beyond the generic. If you use a compliance service’s Policies and Procedures manual, make sure it is customized for your actual practice.
- Policies and procedures aren’t enforced. The written policy looks fine, but the firm isn’t actually following it.
Proving Your Policies Are Actually Enforced
The third deficiency, unenforced policies, is the hardest one to address because intent alone is not enough. SIMAPTIC’s assessment reports provide timestamped records of what your security controls detected and how they responded, mapped to NIST controls. That is the documentation examiners are looking for when they ask to see proof that your plan is actually being followed.
Schedule a Trial Visit Simaptic.aiValidating Your Security Controls
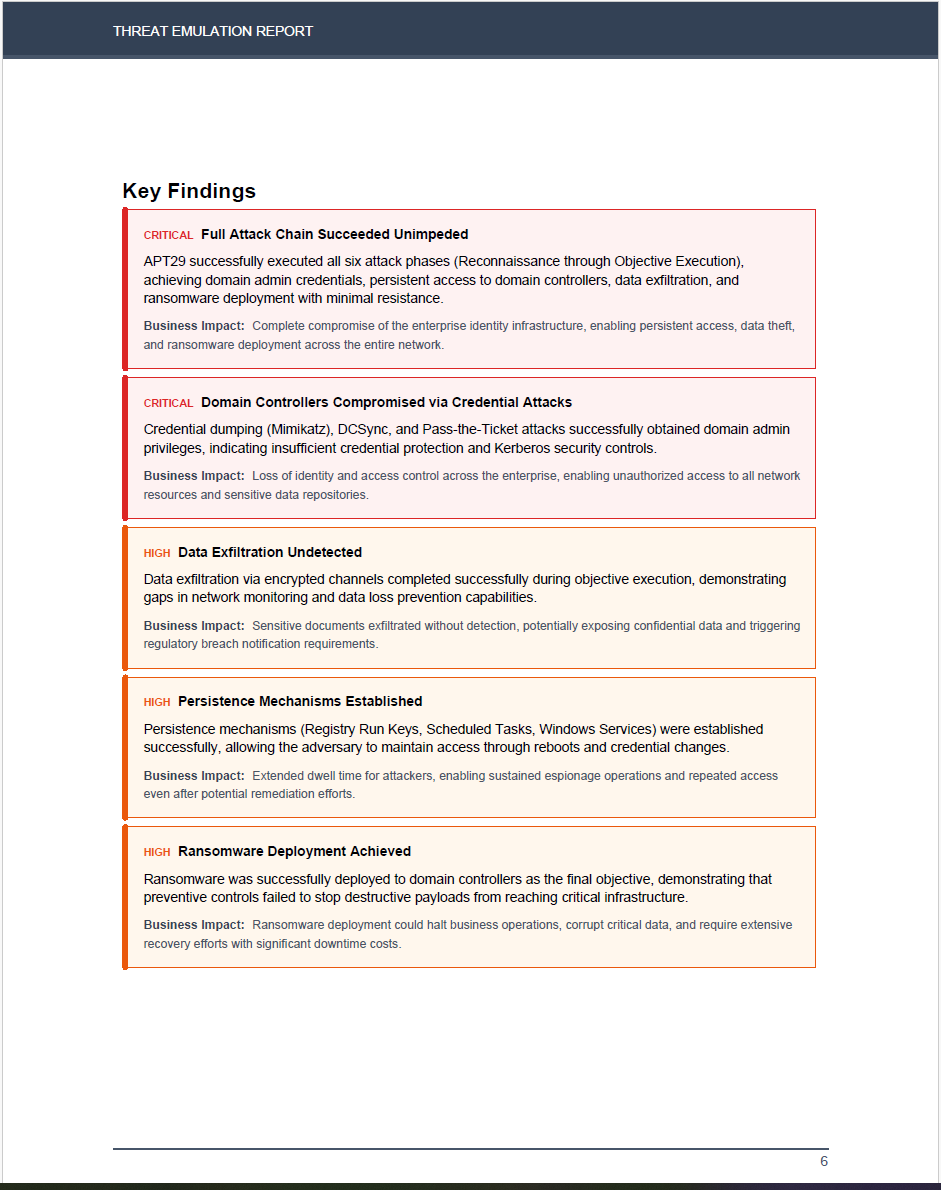
One area the rule implicitly requires, and that examiners will probe, is whether your security controls actually work. It’s not enough to have tools in place. You need to be able to demonstrate they’re functioning as intended.
This means maintaining logs and monitoring reports that would let you determine, in the event of an incident, whether customer information was accessed. If you can’t answer that question with evidence, you have a gap.
It also means producing documentation showing that your policies and procedures work. This is where SIMAPTIC, our AI-driven security assessment tool, comes into play. It will run an autonomous security assessment on your network, providing a report of what security controls were effective and where your shortfalls are. Most importantly, it will map the findings to NIST controls, the framework the SEC recommends. With the written policies outlined in this article and the artifacts from SIMAPTIC, you will be well armed for your Regulation S-P exam.
Where to Start — Recap
If you’re behind, here’s a straightforward sequence:
- Step 1: Document your risk assessment. Identify where client data lives and what risks apply to your environment. Rate them. Note what controls you have in place.
- Step 2: Write your incident response program. Even a simple, well-tailored document that reflects your actual operations is better than nothing. Use the steps above to start.
- Step 3: Review your service provider contracts. Identify which vendors have access to customer information and check whether your agreements include the 72-hour notification requirement. If they don’t, document the gap and start those conversations now.
- Step 4: Test your processes. Leverage SIMAPTIC to run a security assessment on your network. If you have an MSP, did they catch the traffic? Would they have notified you? Did your security tools provide the data you expected? If not, why?
- Step 5: Train your staff. Everyone who touches client data should understand the basics of what the rule requires and what to do if something goes wrong.
As cybersecurity continues to grow in prominence as an area of focus for the SEC, RIAs are at an inflection point where they must start implementing security tools on their networks. Historically, many RIAs have done their best to mitigate cyber risk, but they were often priced out of the market by cyber consultants and security tool providers. SIMAPTIC seeks to change the market by providing a robust and affordable solution to RIAs. June 3rd is close. Getting started now gives you time to get it right.
Ready to Transform Your Business?
Partner with our team of experts to unlock your business’s full potential. Schedule your free consultation and discover how we can help you.
Veteran Owned & Operated
Founded and operated by U.S. military veterans bringing mission-focused discipline to cybersecurity
Successful Projects
our team of consultants brings a wealth of expertise.
Years of Experience
Our strategies have generated over $50 million.